The NIST Cybersecurity Framework was first drafted by the National Institute of Standards and Technology in 2014, with the latest version, version 1.1, following in 2018. It provides a set of guidelines for organizations looking to improve their overall security posture, particularly when it comes to risk management. The core tenets of the Framework can be applied specifically to vulnerability management, as they follow a logical flow from identification to recovery that is applicable to any cyber risk.
Framework Breakdowns
Framework Core
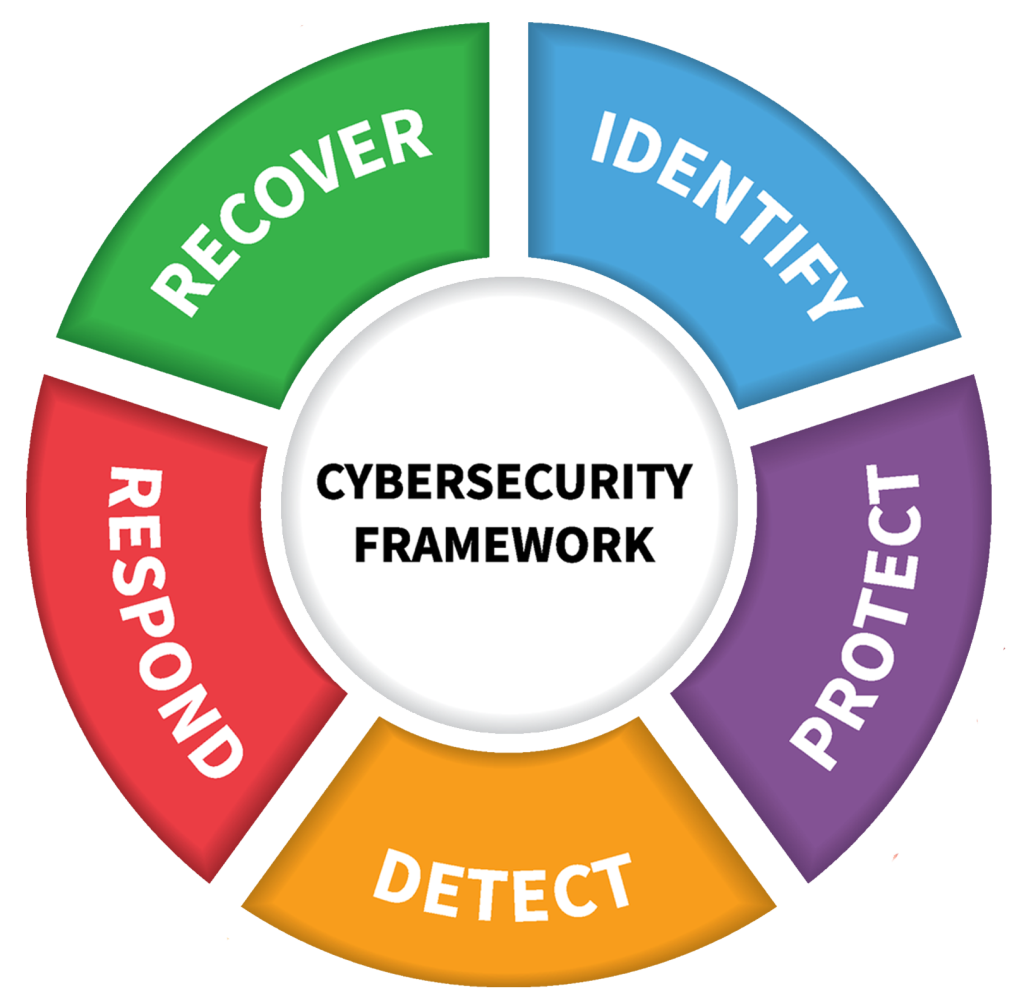
At its highest level, the Framework is broken down into three parts, Core, Profile, and Tiers. Framework Core lays out a series of activities and outcomes broken down into functions, categories, and subcategories. These five functions are:
- Identify: Create organizational understanding to be able to manage risk.
- Protect: Implement safeguards to deter attacks.
- Detect: Develop a plan for identifying cybersecurity events.
- Respond: Put in place an incident response plan in the event of a cybersecurity incident.
- Recover: Have a strategy for restoration of systems and incident resilience.
These five functions are then broken down into 23 categories. Categories are objectives of cybersecurity, such as risk management strategy, mitigation, and data security, to name a few. Within those categories exist 108 subcategories, the most granular level of the Framework. The Framework recognizes that all organizations will have differences in the threats and vulnerabilities they face, so it doesn’t get into the “how” so much as it provides outcome-based statements that, if accomplished, will help create a mature cybersecurity strategy. The vagueness of these statements can be challenging for teams when conducting risk management assessments based on the Framework, as there can be differences in interpretation between the engineers putting the controls in place and the assessors. The key is building awareness and facilitating communication between the teams so the engineers can figure out compliance details in advance if needed.
Framework Tiers
The Framework Tiers describe the degree to which the Framework has been adopted. They are partial, risk-informed, repeatable, and adaptive.
Framework Profile
Organizations interested in using the Framework should create a current profile and a target profile. The current profile maps the Framework to their current cybersecurity status, while the target identifies where they would like to be. The profile takes the Framework and adapts it to the unique organization’s goals and mission, putting the Framework into the context of their business operations.
Framework for Vulnerability Management
The NIST Framework is meant as an overarching cyber strategy, but its process of identify, protect, detect, respond, recover, can be applied specifically to vulnerability management. The Framework itself makes several references throughout the functions and categories to vulnerability management elements, as it is impossible to have a fully functioning cyber program without some form of vulnerability management. Here are some of the subcategories from the Framework that can be incorporated into your vulnerability management process.
Identify
- AM-1: Physical devices and systems within the organization are inventoried and ID.AM-2: Software platforms and applications within the organization are inventoried. When a vulnerability is detected, you need to be able to tie it back to the assets that are impacted. Conducting an asset inventory of both hardware and software will make it easier to map vulnerabilities to the assets that contain them. This is often one of the most challenging steps for organizations because they don’t have knowledge of everything in their environment. Conducting an agentless network scan can help you identify devices that are connected to the network that you may not have in your asset inventory.
- AM-5: Resources are prioritized based on their classification, criticality, and business value. In another post, we discuss the importance of risk-based vulnerability management. Identifying your critical assets will not only come in handy when determining things like segmentation for least privilege, it will also help you prioritize which vulnerabilities to remediate. If you know which assets are the most impactful for your business, when a vulnerability is identified in one of these, you’ll know it should be high on the list for remediation.
- RA-1: Asset vulnerabilities are identified and documented. It’s pretty obvious why this one is essential to vulnerability management. Once you have your asset inventory, you should connect that inventory to the vulnerabilities currently identified in your system, a process known as vulnerability asset mapping. This will help you find the super high priority cross-section of assets that are both high business value and contain severe, exploitable vulnerabilities.
- RA-2: Cyber threat intelligence is received from information-sharing forums and sources. Ingesting threat intelligence is vital for all aspects of security, but it can also improve your vulnerability management program. Modern VM solutions are able to integrate with threat intelligence sources to add much-needed context to vulnerabilities. A vulnerability’s CVSS score is often not representative of the entire picture and can be better evaluated when augmented with real-time threat intelligence. RH-ISAC members have exclusive access to a number of threat intelligence sources, as well as assistance with integrating these feeds into your tech stack. Visit the RH-ISAC website for more information on the benefits of membership.
- RA-5: Threats, vulnerabilities, likelihoods, and impacts are used to determine risk. A modern vulnerability management program takes a holistic view of the organization’s risk profile and prioritizes remediation of risks based not just on the CVSS score, but on additional factors such as the importance of the asset and the conditions required for exploitability.
Protect
- IP-12: A vulnerability management plan is developed and implemented. Having a plan in place helps organize a process and sets clear expectations for responsibilities and outcomes. After the plan is developed and implemented, it should also be reviewed regularly and enforced; otherwise, it will not be effective. Learn more about creating a vulnerability management plan.
Detect
- CM-8: Vulnerability scans are performed. Vulnerability scanning is essential for vulnerability detection. Scanning should cover all aspects of your environment, from network, to operating system, to applications. You may need to rethink your scanning strategy as you move to the cloud and begin to incorporate more API vulnerability scanning and container scanning. Learn more in our blog post on types of vulnerability scanning.
Respond
- AN-1: Notifications from detection systems are investigated. You likely won’t be able to get to every single vulnerability in your environment, but by prioritizing them effectively based on risk, you should be able to respond to the ones that will have the most significant impact. Automation can be useful in this stage. Many vulnerability management systems now either offer the option to initiate remediation workflows from the tool itself or offer integrations with other systems that make remediation easier. Take advantage of these automation capabilities to put in place automatic responses to detected threats to reduce the burden on your security team that is inundated with alerts.
- MI-3: Newly identified vulnerabilities are mitigated or documented as accepted risks. Not every vulnerability is going to be patched. The solution may be a set of controls put in place to minimize the effect, or it may be deemed a low-level vulnerability that doesn’t pose much threat and is therefore pushed to the bottom of the remediation list and accepted. As part of your identify function, you should determine your organization’s risk tolerance, which will inform how many of these accepted vulnerabilities can be lingering in your environment.
Recover
- RP-1: Recovery plan is executed during or after a cybersecurity incident. The goal of vulnerability management is to control vulnerabilities before they are successfully exploited,. However, you’re unlikely to have a 100% success rate. Your vulnerability management plan should address your response in the event that a vulnerability is exploited. If a remediation solution is not available, what other controls can be put in place to reduce the impact?
- IM-1: Recovery plans incorporate lessons learned. If a vulnerability is successfully exploited, what caused this to occur? Are there improvements that could be made in your detection or remediation processes that could prevent a similar incident?
You can use these subcategories of the Core Framework to guide your vulnerability management plan. The Framework Tiers and Profiles can be used to determine how mature your VM program is and help you set goals for improvement. You can find the full Framework on the NIST website.
RH-ISAC members have exclusive access to Member Exchange, our community discussion platform where retail and hospitality cybersecurity professionals collaborate and exchange knowledge. Join the Vulnerability Management Working Group to participate in discussions and exchange of best practices. Not a member? Learn more about RH-ISAC membership.