In the last few years, ransomware planning has become a priority for cyber teams, with 85% of organizations in Fortinet’s 2021 Global Threat Landscape Report reporting ransomware as their biggest security concern. Similarly, ransomware resilience planning topped the list of CISO initiatives for 2022 in RH-ISAC’s recent Benchmark Report. Ransomware resilience planning tends to focus on a few key areas such as security awareness, identity and access management, or application security. Still, an often overlooked but crucial prevention tactic is sharing of threat intelligence.
Collaboration is Key
Threat actors are not operating inside a vacuum. Initial access brokers are selling credentials to ransomware-as-a-service providers who lease their platform and product to other groups of cyber criminals. If the enemy is collaborating, it only makes sense that our own cyber teams should be collaborating to stop them.
Information Sharing and Analysis Centers (ISACs) exist to provide a safe space for business competitors to share threat intelligence for the collective security of their sector. The first ISACs were formed in 1999 as a result of Presidential Decision Directive-63 (PDD-63), which required the creation of an ISAC for critical infrastructure sectors. The RH-ISAC, which was founded in 2014, serves as the ISAC for retail, hospitality, and travel. In addition to providing members with threat intelligence, ISACs participate in programs such as the Department of Homeland Security (DHS) Cyber Information Sharing and Collaboration Program (CISCP). Through this program, RH-ISAC provides threat information to DHS affiliated agencies including the FBI, United States Secret Service, United States Computer Emergency Readiness Team (US-CERT), and others.
RH-ISAC Facilitates Intelligence Sharing
RH-ISAC provides Core Member companies with access to a variety of intelligence-sharing platforms, including listservs, a Member Exchange community, Slack channels, and weekly intelligence calls. Here, analysts from across the industry share actions their teams are taking to more effectively monitor and protect their networks, data, and applications, as well as TTPs and IOCs they’ve observed in their environments.
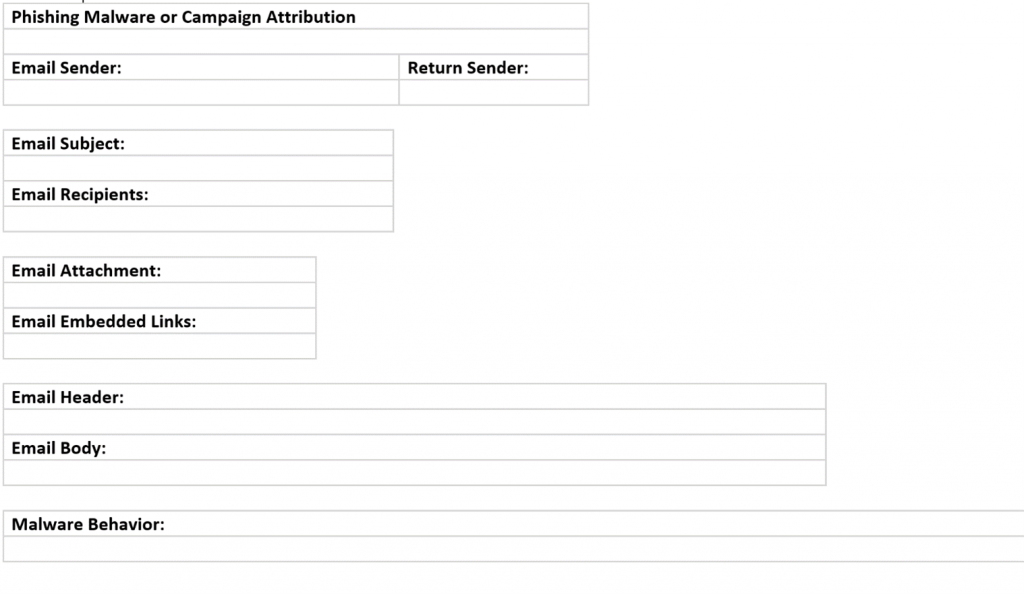
These notifications provide key information about phishing attacks, ATO attempts, malware, and other observed threats that can alert you to a potential breach before it occurs, improving your threat detection capabilities.
Information from across these sharing channels, as well as intel collected from RH-ISAC’s monitoring tools, is rolled up into daily reports and can be ingested by members via a complimentary TruStar-Splunk integration. Now, not only do you have access to your own organization’s monitoring capabilities, you also have insights from the cyber teams of 200+ other retailers, significantly expanding your visibility into the threat environment. Plus, all sharing data is tracked and summarized in quarterly trend reports, which provide a higher-level overview of the types of threats members are worried about.
For example, the most recent RH-ISAC Community Landscape Enterprise Analysis Report provided members with the most common malware strains identified over the course of a three-month period. Many of these strains, including XingLocker are forms of ransomware, or like Dridex and Qakbot, are precursors to ransomware.
Without shared intelligence, you may not even know what you should be looking for, making it hard to detect before a ransomware attack occurs. Being aware of the threat landscape and staying up to date on the best practices used to defend against these threats is one of the many benefits of collaboration.
Visit the RH-ISAC website to learn more about intelligence sharing and RH-ISAC membership. Want to learn more about preventing ransomware attacks? Download RH-ISAC’s ransomware resilience resource guidep
