Executive Summary
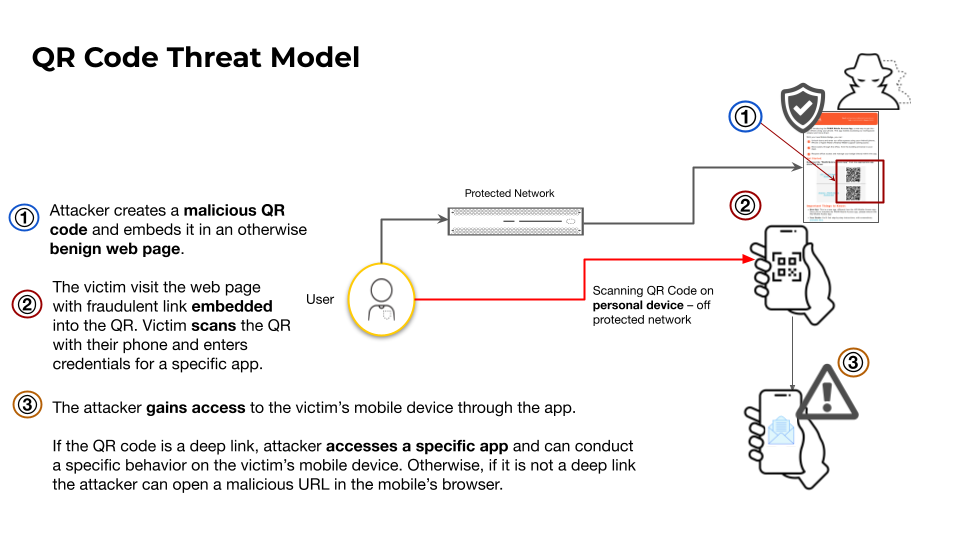
With QR codes having a notable presence in our everyday lives, some people instinctively scan them without hesitation. But QR codes are also a vector for attack. QR codes enable attackers to bypass organizational security by exploiting the weaker controls of personal mobile devices. By doing this, they can trick users into scanning codes and interacting with malicious destinations outside the corporate security perimeter.
Over the past several months, we have tracked campaigns that used QR codes for phishing (known as quishing) and scams. Our telemetry reveals an average of over 11,000 detections of malicious QR codes each day. Investigating these detections, we found that attackers are leveraging QR code shorteners, in-app deep links and direct downloads to bypass people’s awareness and security controls.
Technical Analysis:
Our research explores the misuse of QR codes in today’s threat landscape, covering three areas of concern:
- QR codes using URL shorteners to disguise malicious destinations
- QR codes using in-app deep links to steal account credentials and take control of a victim’s apps
- QR codes attempting to bypass app store security by linking to direct downloads of malicious apps
The popularity of QR codes has led to their use by attackers. In our offline web crawlers, we currently find an average of 75,000 detections of QR codes each day, with 15% of these pages containing QR codes leading to malicious links. This represents an average of over 11,000 detections of malicious QR code use each day.
We looked beyond the recognized risks of QR codes. While straightforward QR code web-based attacks remain a threat, our focus shifted to understanding how attackers are leveraging the following trends to remain evasive to both victims and security controls:
- QR code shorteners
- In-app deep links (special URLs that allow people to open specific content within a mobile app)
- Direct app file downloads
The following image further illustrates our conceptualization of the QR code threat model:
Retail and Hospitality Perspective:
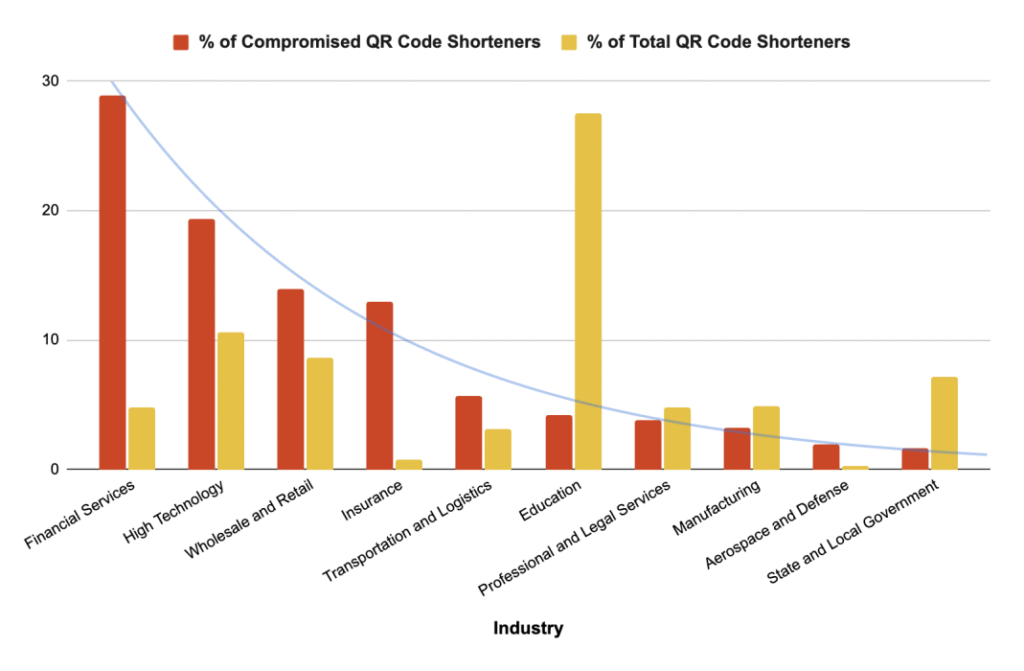
Retail and wholesale was the third most targeted industry for QR code-based attacks, accounting for 14% of observed cases as shown in the image below.
Account Takeover (ATO) continues to be a type of attack frequently leveraged by financially-motivated threat actors to infiltrate the customer accounts of retail and hospitality organizations. As noted in our report, ATO is one of the attack chain scenarios possible through the usage of in-app deep links. Successful ATO attacks not only lead to the short term loss of gift card funds and/or loyalty points but can also erode consumer confidence in a company over time which can have significant financial and reputational implications.
RH-ISAC members should work closely with their security awareness and training teams to develop tailored training for end users on the evolving nature of QR code threats and be extra vigilant of such activities during peak retail and hospitality seasons.
Indicators of Compromise:
https://unit42.paloaltonetworks.com/qr-codes-as-attack-vector/