Summary
A fraudulent website impersonating Avast’s visual identity targets French-speaking users by claiming a non-existent €499.99 charge requires a refund, according to a new report by Malwarebytes Labs. The operation utilizes a sophisticated blend of urgency, real-time live chat support via Tawk[.]to, and dynamic page elements to harvest full credit card details and personal information.
Technical Analysis
The phishing infrastructure employs a single line of JavaScript to fetch the visitor’s local system clock, ensuring the fake transaction date always appears current. To ensure the collection of high-quality data, the credit card input field implements the Luhn algorithm to validate card numbers before submission. Upon completion, the browser executes a POST request to a backend script designated send[.]php, which transmits the harvested PII and payment data as a JSON object. The integration of the Tawk[.]to widget, account ID 689773de2f0f7c192611b3bf, allows operators to monitor visitor behavior and provide live prompts to users who might hesitate during the data entry process.
The reuse of this specific account ID in other impersonation refund scams indicates that a single threat group or service provider manages the “live support” backend for multiple fraudulent brands simultaneously. In these parallel campaigns, the actors could maintain the same €499.99 price point and “Luhn-validated” payment forms to ensure consistency across their operations. By utilizing a single Tawk.to instance, the operators can centralize their social engineering efforts, allowing a small team of “agents” to handle victim inquiries from various phishing sites through one unified dashboard.
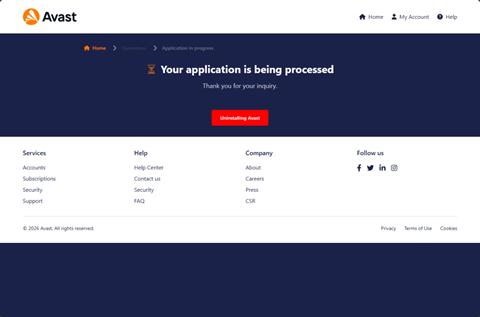
This approach shifts the threat from a static credential harvester instance to a broader fraud operation that manages identity verification through a multi-stage modal interface. To bolster the visual check, the site pulls the official Avast logo directly from the brand’s own content delivery network. After the data is successfully dispatched, the application redirects the victim to a confirmation page that suggests uninstalling existing security software to reduce the likelihood of immediate incident discovery.