Summary
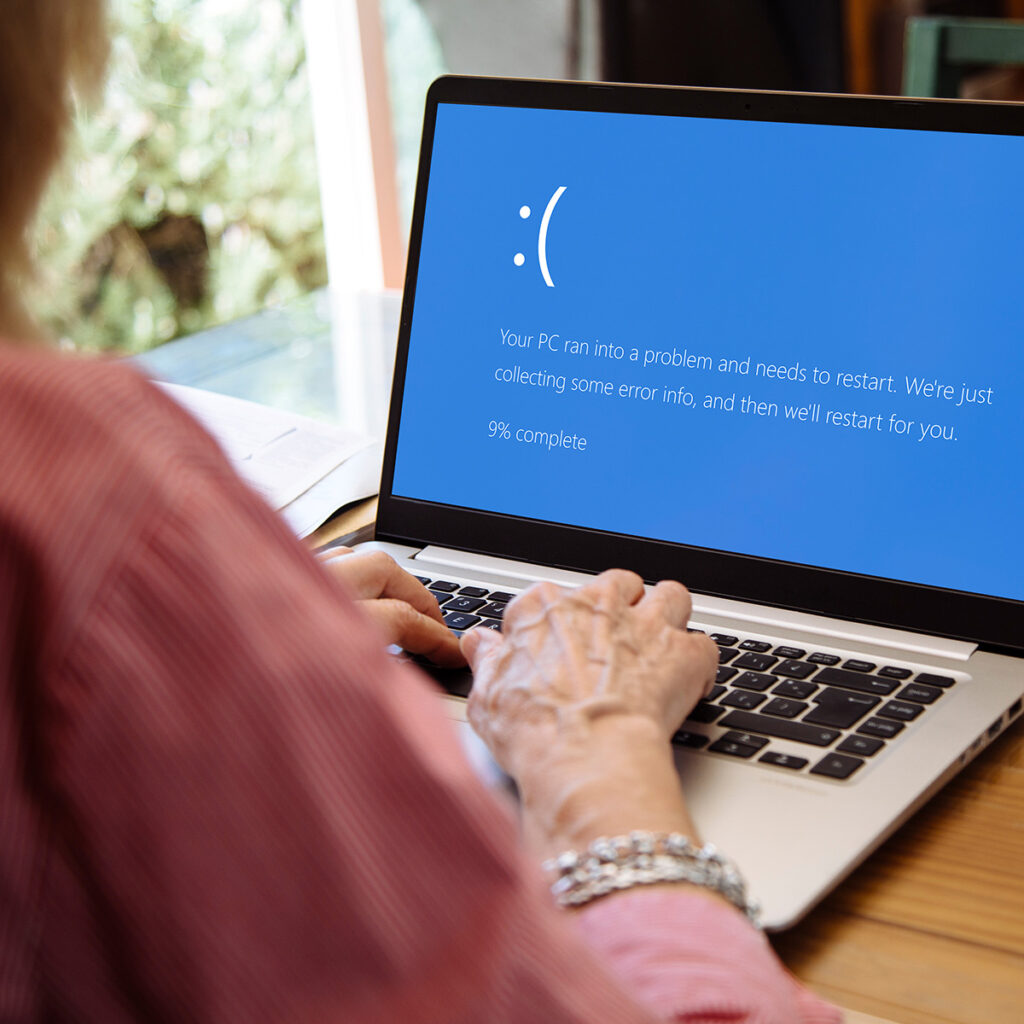
Securonix researchers have identified a new malware campaign, dubbed PHALT#BLYX, actively targeting the hospitality sector with a multi-stage infection chain. Threat actors leverage a “ClickFix” social engineering tactic, using fake reservation emails and deceptive “Blue Screen of Death” (BSOD) pages to deceive victims into executing malicious PowerShell commands. This campaign notably bypasses defenses by utilizing the trusted Microsoft Build Engine to compile and execute a customized, heavily obfuscated DCRat payload linked to Russian threat actors. The final payload enables full remote access, process hollowing, keylogging, and the ability to drop secondary malware, posing a emerging threat to organizations during post-holiday shopping seasons.
Sector Impact
Hospitality organizations are the primary targets, facing heightened risks from high-value fake reservation lures designed to panic staff into bypassing security protocols. A successful infection could grant attackers persistent remote access to reservation systems and payment data, potentially leading to data breaches and operational disruption during critical business periods. As such, RH-ISAC Core Members should review the intelligence in this alert and ingest the included Indicators of Compromise, provided by Securonix, included below.
Analysis
The infection chain utilizes a “ClickFix” technique where a JavaScript-controlled fake BSOD prompts the victim to paste a malicious PowerShell script directly into the Windows Run dialog, bypassing browser-based security controls. This script initiates a “Living off the Land” sequence by downloading an XML-based project file (v.proj) and invoking the trusted MSBuild.exe utility to compile and execute embedded C# code.
To ensure evasion, the malware preemptively modifies Windows Defender settings via Add-MpPreference, whitelisting the C:\ProgramData staging directory and specific file extensions before dropping the final payload. Privilege escalation logic dictates the infection path; if running as a standard user, the script enters a loop of Start-Process calls with the -Verb RunAs argument to spam UAC prompts until administrative access is granted.
The final payload, identified as a modified DCRat, establishes persistence by placing a .url internet shortcut file in the Startup folder that points to a local executable via the file:/// protocol. Reverse engineering of the binary reveals Costura.Fody packing and AES-256 encryption using PBKDF2 key derivation, while embedded Cyrillic debug strings confirm the involvement of Russian-speaking developers.
The C2 communication employs MessagePack serialization over port 3535 to domains such as asj77[.com, facilitating encrypted command-and-control capabilities for secondary payload injection.
Indicators of Compromise
Securonix researchers included the following Indicators of Compromise, which are included below for RH-ISAC Member awareness.
File Paths:
%ProgramData%\v[.]proj
%ProgramData%\staxs[.]exe
C:\Windows\Temp\tybd7[.]exe
%Startup%\DeleteApp[.]url
%Startup%\update[.]lnk
C2 and Infrastructure:
Oncameraworkout[.}com/ksbo
low-house[.]com
2fa-bns[.]com
asj77[.]com
asj88[.]com
asj99[.]com
194[.]169[.]163[.]140
193[.]221[.]200[.]233
13[.]223[.]25[.]84
wmk77[.]com
8eh18dhq9wd[.]click
Port: 3535
Analyzed Files/Hashes:
Ps1[.]ps1
cd3604fb9fe210261de11921ff1bea0a7bf948ad477d063e17863cede1fadc41
payload_1[.]ps1
13b25ae54f3a28f6d01be29bee045e1842b1ebb6fd8d6aca23783791a461d9dd
[.]ps1
9fac0304cfa56ca5232f61034a796d99b921ba8405166743a5d1b447a7389e4f
v[.]proj
cd3604fb9fe210261de11921ff1bea0a7bf948ad477d063e17863cede1fadc41
v[.]proj[.]ps1
9fc15d50a3df0ac7fb043e098b890d9201c3bb56a592f168a3a89e7581bc7a7d
Stub[.]exe/Staxs[.]exe/tydb7[.]exe
bf374d8e2a37ff28b4dc9338b45bbf396b8bf088449d05f00aba3c39c54a3731
Stub[.]exe
11c1cfce546980287e7d3440033191844b5e5e321052d685f4c9ee49937fa688
Stub[.]exe
07845fcc83f3b490b9f6b80cb8ebde0be46507395d6cbad8bc57857762f7213a
Stub[.]exe
08037de4a729634fa818ddf03ddd27c28c89f42158af5ede71cf0ae2d78fa198
Stub[.]exe
2f3d0c15f1c90c5e004377293eaac02d441eb18b59a944b2f2b6201bb36f0d63
Stub[.]exe
33f0672159bb8f89a809b1628a6cc7dddae7037a288785cff32d9a7b24e86f4b
Stub[.]exe
6bd31dfd36ce82e588f37a9ad233c022e0a87b132dc01b93ebbab05b57e5defd
Stub[.]exe
1f520651958ae1ec9ee788eefe49b9b143630c340dbecd5e9abf56080d2649de
DeleteApp[.]url
9c891e9dc6fece95b44bb64123f89ddeab7c5efc95bf071fb4457996050f10a0
Wwigu[.]exe
e68a69c93bf149778c4c05a3acb779999bc6d5bcd3d661bfd6656285f928c18e
Wwigu[.]exe
18c75d6f034a1ed389f22883a0007805c7e93af9e43852282aa0c6d5dafaa970
Lbpyjxefa[.]dll
91696f9b909c479be23440a9e4072dd8c11716f2ad3241607b542b202ab831ce