Executive Summary
Infrastructure provider Vercel disclosed a significant security incident, stemming from a compromise of the third-party AI tool Context[.]ai. A highly sophisticated threat actor leveraged a hijacked OAuth token from a Vercel employee to gain unauthorized access to internal environments and non-sensitive environment variables.
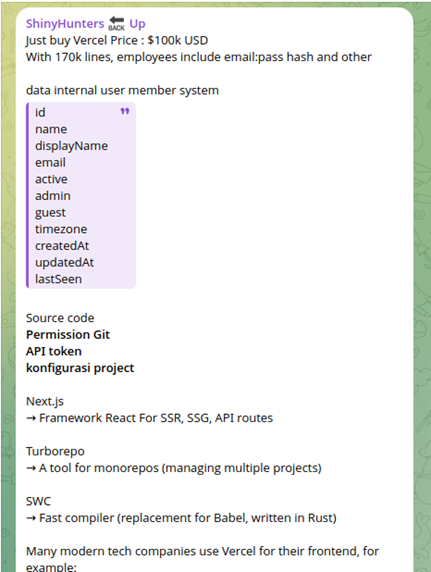
ShinyHunters has claimed responsibility for the breach, allegedly offering the exfiltrated data for sale on illicit forums for $2 million.
Vercel is currently working with Mandiant and law enforcement to remediate the impact, which primarily affects a limited subset of customer credentials and unencrypted secrets.
Technical Analysis
According to an official statement from Vercel, The intrusion sequence began in February 2026 when a Context.ai employee downloaded a malicious video game exploit, leading to a Lumma Stealer infection on their workstation. This initial malware deployment harvested Google Workspace credentials and sensitive logins for critical infrastructure services including Supabase, Datadog, and Authkit. By gaining control of the support@context[.]ai account, the adversary successfully bypassed security controls to obtain a valid OAuth token belonging to a Vercel employee. This specific token originated from a Vercel enterprise account that had granted “Allow All” permissions to the Context.ai “AI Office Suite” application. Vercel’s internal OAuth configurations permitted these broad permissions, enabling the threat actor to pivot directly into the company’s enterprise Google Workspace environment. Once inside, the attacker identified and exfiltrated environment variables that were not flagged as “sensitive,” a categorization that lacks the mandatory encryption applied to protected secrets. The adversary utilized a Google OAuth application ID to maintain their foothold and execute rapid system reconnaissance.
Context.ai said it immediately alerted all impacted customers and provided them with the necessary steps they needed to take. It did not reveal how many customers were affected by the breach.
Indicators of Compromise
Vercel has provided the Google OAuth application ID utilized to maintain their attack, which can be found below:
110671459871-30f1spbu0hptbs60cb4vsmv79i7bbvqj[.]apps[.]googleusercontent[.]com