Executive Summary
Unit 42 has responded to numerous incidents since February 2026 involving data theft and extortion across various industries. We attribute a specific portion of this financially-motivated activity with moderate confidence to the activity cluster CL-CRI-1116, which overlaps with public reporting on BlackFile, UNC6671 and Cordial Spider.
This blog is designed to provide RH-ISAC members with unique insights from Unit 42 investigations, along with defensive recommendations to counter this emerging threat activity.
Unit 42 Insights
While this threat activity first emerged in January 2026, Unit 42 assesses with moderate confidence that the attackers behind CL-CRI-1116 are likely associated with a collective known as “The Com,” which we have reported on extensively in recent years. The attackers behind CL-CRI-1116 do not rely on custom malware or tooling. Rather, they focus on Living Off the Land through misuse of Application Programming Interfaces (APIs) and other legitimate internal resources.
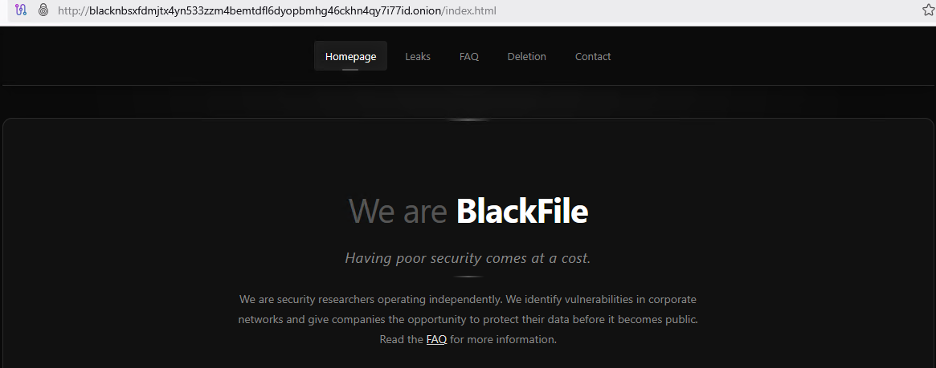
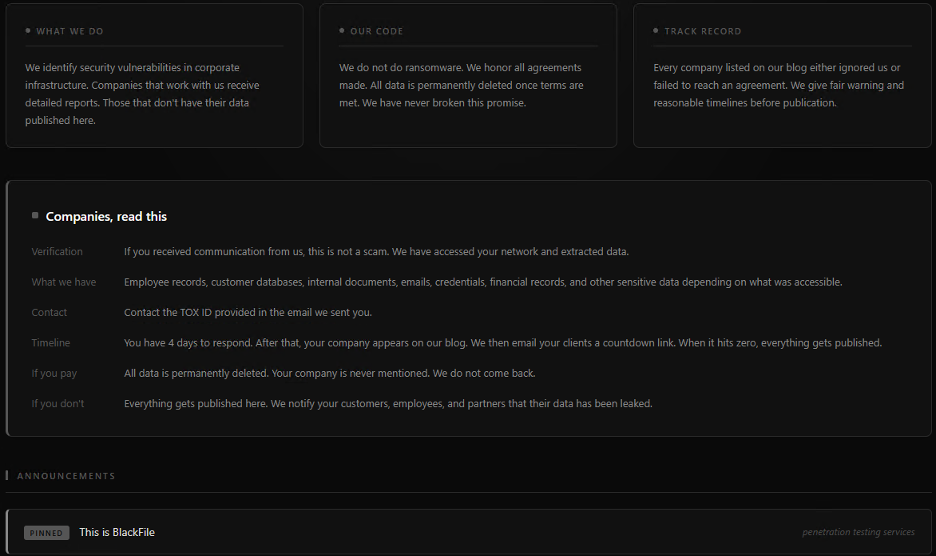
The attackers behind CL-CRI-1116 created their own data leak site (DLS) to extort victims, as shown below in Figures 1 and 2.
The following section details what a typical attack lifecycle looks like for CL-CRI-1116.
Resource Development (T1583.001):
CL-CRI-1116 attacks consist of phishing pages resembling legitimate corporate sites, usually Single Sign-On (SSO), that are designed to capture user credentials upon input. They also utilize antidetect browsers and residential proxies to mask their geographic location and bypass basic IP-based reputation filters.
Initial Access (T1566.004):
The attackers behind CL-CRI-1116 use voice-based phishing (vishing) from spoofed Voice over Internet Protocol (VoIP) numbers or fraudulent Caller ID Names (CNAM) as a social engineering technique, typically posing as IT support staff.
The attackers use this technique to entice employees into providing their credentials and time-based one-time passwords (TOTP) into the phishing pages they created.
Persistence (T1098.005):
CL-CRI-1116 attackers may register a device under their control as a mechanism to bypass Multi-Factor Authentication (MFA) in Identity and Access Management platforms once an employee account is successfully compromised.
The attackers also maintain access by moving laterally from standard employee accounts to high-privileged accounts. They scrape internal employee directories to obtain contact lists for executives. By compromising these senior accounts via further social engineering, they gain persistent, broad-spectrum access to the environment that mirrors legitimate executive session activity.
Collection (T1213):
CL-CRI-1116 activity focuses on data discovery within Software as a Service (SaaS) environments and internal repositories. They abuse Microsoft Graph API permissions (specifically Sites.Read.All) to scrape SharePoint sites and utilize SaaS internal search functions (such as Salesforce). They prioritize high-value targets by searching for specific string literals such as “confidential” and “SSN” within files and reports.
Exfiltration (T1567.002):
CL-CRI-1116 attacks exfiltrate data directly through the browser or via API exports. By leveraging Salesforce API access and standard SharePoint download functions, the attackers move large volumes of data – including CSV datasets of employee phone numbers and confidential business reports – to attacker-controlled infrastructure. This is often done under the guise of legitimate SSO-authenticated sessions to avoid triggering simple user-agent alerts.
CL-CRI-1116 may also consist of file-sharing services like LimeWire or MEGA to stage stolen data.
Impact (T1657):
CL-CRI-1116 has both randomly generated alphanumeric Gmail addresses and compromised employee email accounts from targeted organizations to send aggressive ransom demands, typically in the seven-figure range.
As an added leverage tactic, the attackers will use SWATting targeting company personnel, including C-suite executives, to pressure victims into paying their ransom demands.
RH-ISAC Recommendations
CL-CRI-1116 activity has been actively targeting the retail and hospitality space since February 2026, specifically leveraging vishing attacks impersonating IT helpdesk personnel in combination with phishing login sites to steal credentials.
To mitigate the success rate of these tactics, organizations are advised to focus on security policies, managing multi-factor identity verification for callers, protocols around what information can be shared in calls, and what IT support actions can be completed in a single call without escalation to management. Additionally, security awareness training for frontline phone staff can be effective, focused on simulation-based scenarios and identifying signs of social engineering, such as vague answers to identity questions and attempts to create a high-pressure request for immediate action.
Many retail and hospitality organizations report an improvement in security posture against vishing IT impersonation attempts by combining policy review/changes, staff education, and technical security controls such as VoIP log analysis and MFA configurations.
Indicators of Compromise
User-Agent: Python-requests/2.28.1
24.177.37[.]97 |
35.139.72[.]161 |
37.19.210[.]9 |
72.180.124[.]192 |
111.235.93[.]125 |
112.207.101[.]227 |
112.207.108[.]30 |
112.209.151[.]78 |
119.111.248[.]227 |
136.158.24[.]160 |
136.158.27[.]101 |
136.158.27[.]72 |
136.32.210[.]197 |
136.35.103[.]90 |
146.70.172[.]228 |
179.43.185[.]226 |
184.93.0[.]17 |
185.193.127[.]130 |
185.231.33[.]62 |
199.127.61[.]200 |
208.131.130[.]67 |



