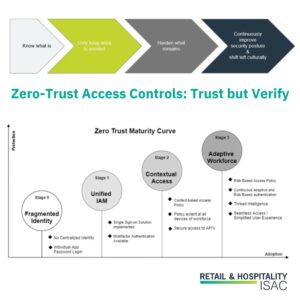
Zero-Trust Access Controls: Trust but Verify
From the onset, access control is the most dynamic pillar in the ZTA implementation process. New accounts need to be created for legitimate business use, accounts likely need varying degrees of access, and account revocation for individual accounts and a mass list is always a concern. Identity and Access Management (IAM) Basics The quest towards…
Read More